The way we deliver health care, build self-driving cars and even plan for retirement stand to become significantly more effective in the next decade with the impending emergence of quantum computing. Approaching problem-solving in a fundamentally new way, these sophisticated machines can process vast numbers of calculations simultaneously and generate results exponentially faster than today’s computers.
And yet, as with every new technology, quantum computing will also pose some risks. Primarily, our society’s current information and communication technology (ICT) architecture, which uses conventional public-key cryptography, is vulnerable against attacks by quantum computers. This means organizations’ sensitive data – personal information, intellectual property, credit card data, health records – could be leaked or corrupted.
“Today’s most commonly used cryptographic measures will be no match for the power of quantum computers,” says Atefeh Mashatan, founder and director of the Cybersecurity Research Lab at Ryerson University’s Ted Rogers School of Management. “The integrity and confidentiality of our important information, which is key to the functioning of our economy, needs to be protected against these highly sophisticated computers.”
A leading cybersecurity expert and former senior information security consultant for CIBC, Mashatan is on a mission to help the ICT industry in Canada prepare for the rise of quantum computers. She is facilitating the transition to quantum-resistant cryptography with “Strategic Implications of Quantum Computing for Enterprises,” a project that arms organizations with knowledge about the nature of this complex threat and enables them to prepare for and respond to quantum cyber attacks.
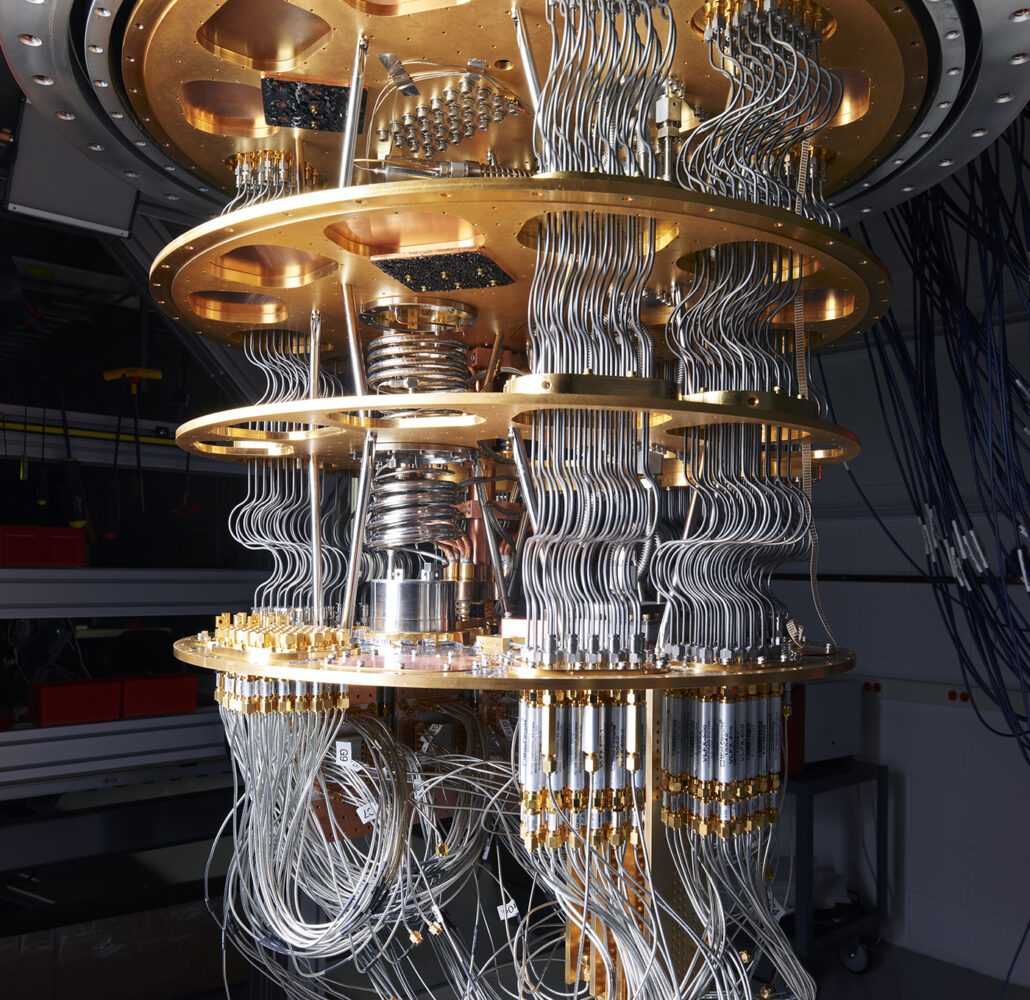
How quantum computing works
Traditional computers work on millions of lines of code on computer chips featuring binary digits, or bits, with a value of either one or zero. The introduction of quantum mechanics to computing has led to quantum bits, or “qubits,” which can represent a superposition of a one and a zero. This capability allows a computer to solve a certain class of problems dramatically faster than the best classical computers. How much faster? A quantum computer in China recently took minutes to complete a calculation that would have taken a supercomputer of comparable size two billion years.
This new computing paradigm holds immense promise for the field of medicine by allowing for faster analysis of medical images, which could lead to more accurate diagnoses and better understanding of drug sensitivities at the cellular level – a boon for personalized medicine. More broadly, quantum computing may yield efficiency advantages in areas such as basic scientific research; artificial intelligence and machine learning; financial modelling; traffic optimization; and climate change forecasting.
Preparing for quantum cyber threats
Commercially available quantum computers are still at least five to 10 years away, though research and development by academics, governments and companies such as Microsoft, Google, IBM, Intel and D-Wave Systems are accelerating the pace of innovation. In response, Mashatan and others are developing a quantum readiness roadmap to prepare the organizations for an impending transition. Mashatan also contributes to these efforts as a member of the academic steering committee of Quantum-Safe Canada, a not-for-profit organization focused on advancing quantum-ready cryptography research and innovation.
In the meantime, Mashatan says, organizations must start taking steps now to modernize their information security infrastructure. She noted in the May 2020 edition of Management Information Systems Quarterly Executive that IT managers must establish a governance structure for addressing this issue; conduct a quantum risk assessment; evaluate their firm’s current cryptographic footprint; and develop an appropriate transition plan.
“If and when an attack-capable quantum computer is available, the attacker who has harvested encrypted information can decrypt and achieve whatever malicious goal they have in mind,” Mashatan says. “So it is imperative for organizations to understand the sensitivity and shelf life of their important assets, and to decide now which ones need complementary protection against the quantum threat.”